Patrick Denis > Cisco
Cisco
admin
May 18, 2016
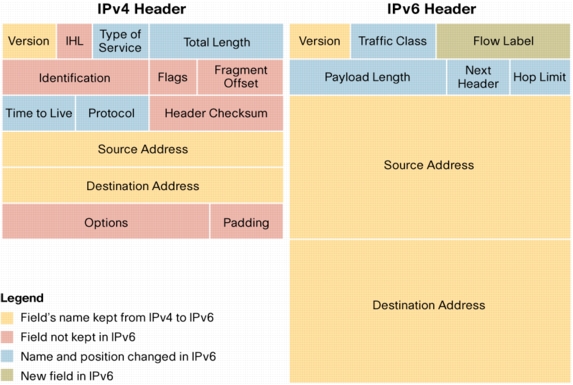
The IPV4 Option is in the IHL ‘Internet Header Length’ Field, it is a minimum value of 5 and if it is that mean that there is no options configured and we have a 20 bytes ip header. The Internet…
Read more
admin
May 14, 2016
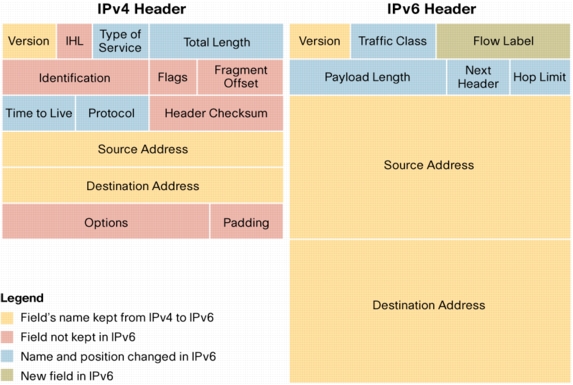
IP Maximum Transmission Unit (MTU) IPv4 routers will fragment automatically to fit within the MTU (unless DF – Don’t Fragment option is set). IPv6 routers will not fragment, and will drop packets that are larger than MTU. IPv4 requires that…
Read more
admin
May 14, 2016
Time to live (TTL) is a hop limit set to limit the lifetime of data on a network. This prevents data from looping endlessly. Each hop decrements the value by 1. If TTL reaches 0, the data is discarded and…
Read more
admin
May 13, 2016
ICMP offers troubleshooting facility as well as error reporting for the packets 0 1 2 3 0 1 2 3 4 5 6 7 8 9 0 1 2 3 4 5 6 7 8 9 0 1 2…
Read more
admin
May 13, 2016
From what i understand is that a micro-burst occurs when a specific amount of data (in bytes) is exceeded in a given time interval. Example when you do a show interface | in Input and by repeat this command the numbers…
Read more
admin
May 13, 2016
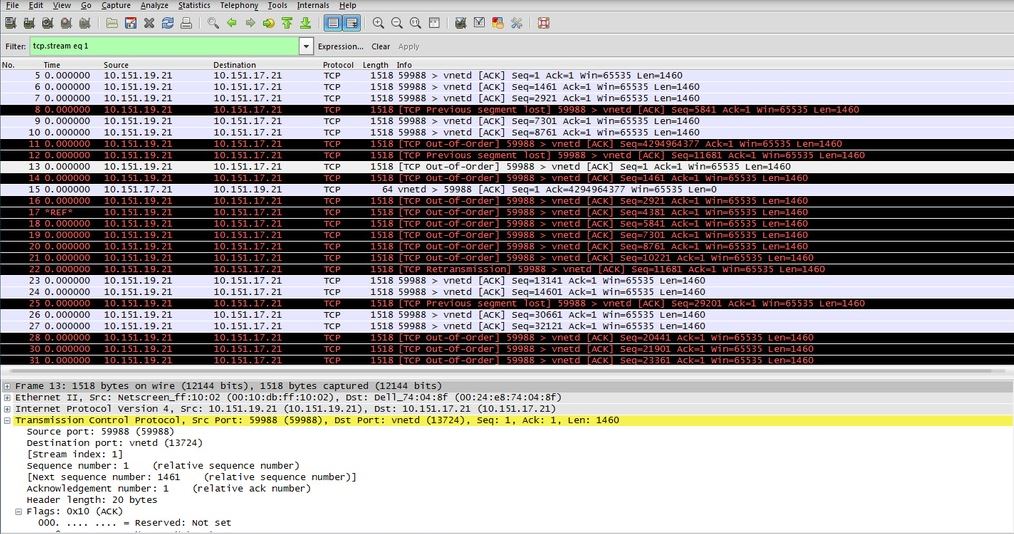
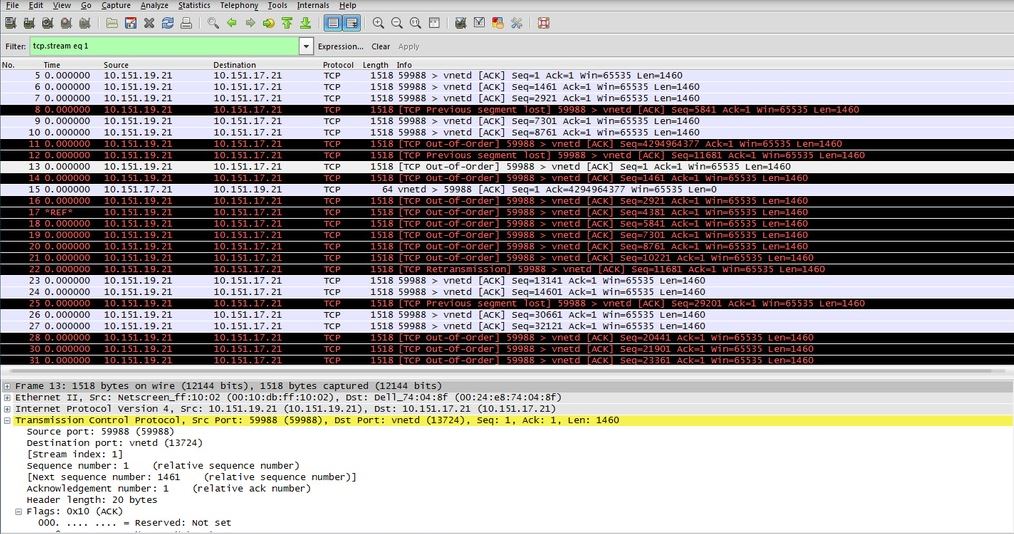
RFC 793 ( pages 20 and up ) TCP is the protocol that make sure that the transmission is done without losing any packet by going through a set of operation for the order of transmission and for any duplication detection….
Read more
admin
May 13, 2016
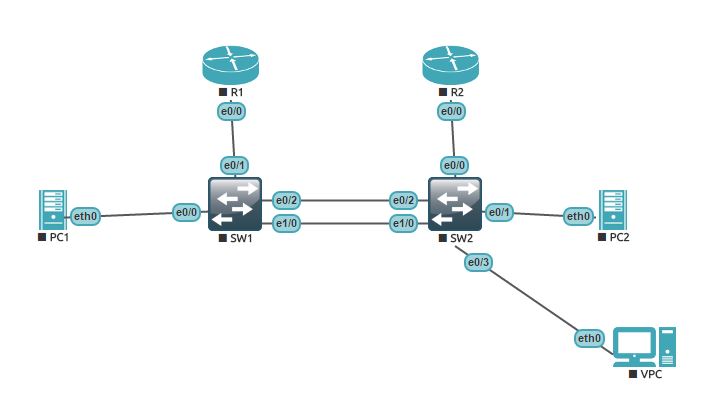
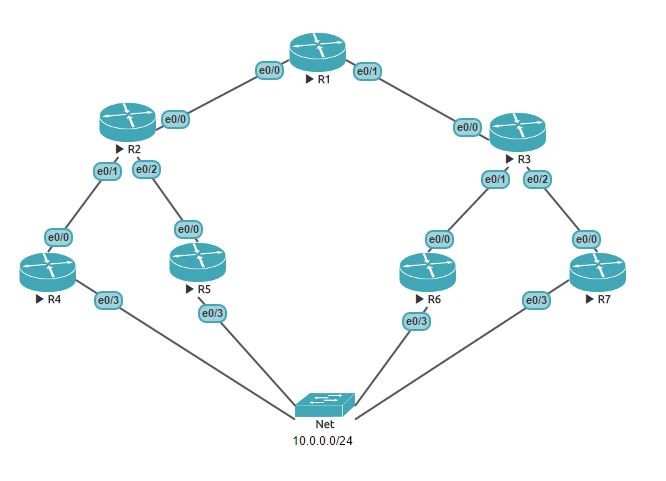
Asymmetric routing is when Packets follow different paths depending on the direction. Asymmetric routing is one of the two most common causes of flooding.
admin
May 13, 2016
This happen when the switch does not have the destination mac address in his Layer 2 table. It is call an Unknown unicast , it Floods frame out all interfaces in the same VLAN, except the interface on which the frame was received….
Read more
admin
May 11, 2016
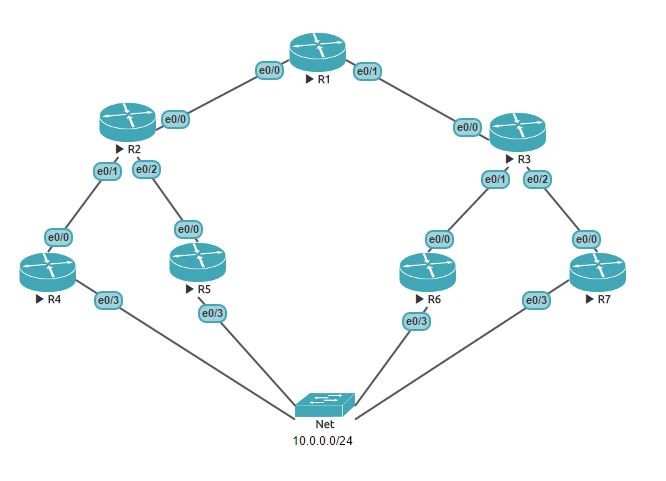
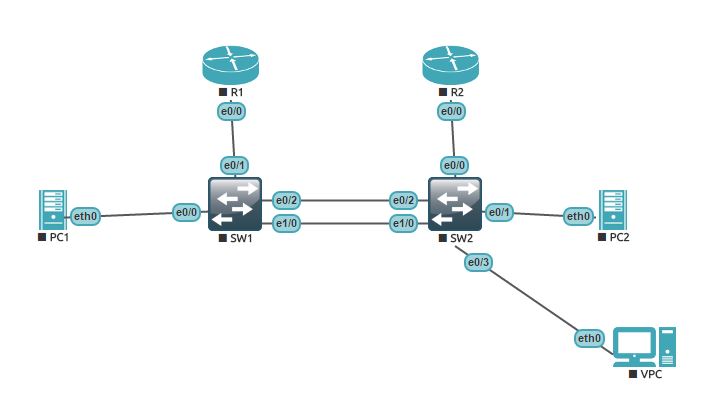
Lab ready will now try to understand that carefully since i don’t understand at alllllllllllllllll 😛 http://ciscocramfest.blogspot.ca/2014/12/notes-cef-polarization.html no comprende !!! http://www.cisco.com/c/en/us/support/docs/ip/express-forwarding-cef/116376-technote-cef-00.html http://www.cisco.com/c/en/us/support/docs/ip/express-forwarding-cef/116376-technote-cef-00.pdf http://wiki.kemot-net.com/igp-load-sharing-cef-polarization
admin
May 10, 2016
Ref: http://www.cisco.com/c/en/us/td/docs/ios-xml/ios/ipswitch_cef/configuration/15-mt/isw-cef-15-mt-book/isw-cef-load-balancing.html CEF Load-Balancing Cisco Express Forwarding load balancing is based on a combination of source and destination packet information; it allows you to optimize resources by distributing traffic over multiple paths. You can configure load balancing on a per-destination or…
Read more